News Analysis: Acquisition Of Fiberlink Fills Key Gap In IBM's One-Stop Mobile First Strategy

IBM Acquires Fiberlink (MaaS360) For Mobile Management And Security
On November 13th, Blue Bell, PA based Fiberlink Communications signed a definitive agreement to be acquired by Armonk, NY based IBM for an undisclosed sum. Fiberlink has over 3500 clients in key verticals such as financial, retail, public sector, education, and healthcare. IBM expects to close the acquisition at year's end. The deal is significant to customers because:

- IBM is committed to deliver one stop mobility via acquisitions and organic growth. IBM has made eight acquisitions in the last 18 months (see Figure 1). In 2012, IBM acquired Emptoris, Worklight, and Tealeaf Mobile. Urban Code, The Now Factory, Xtify, Trusteer, and Fiberlink formed the 2013 acquisition list. Along the way in 2012, IBM launched three mobile offerings: IBM Endpoint Manager for mobile devices, IBM Connections Mobile, and IBM Security Access Manager for Cloud and Mobile. In 2013, IBM made the IBM Mobile First announcement along with the IBM Message Sight solution.
Point of View (POV): Mobile is the key onramp to digital business. The average individual is no further than three feet from their devices and always on 14 to 15 hours a day. Unfortunately, today's mobile offerings often are piecemeal and incomplete. IBM has made a strategic bet to provide the end to end mobile first life cycle. IBM sees four key entry points for mobile: build, engage, transform, and optimize. Worklight and Urban code addresses build. IBM Connections Mobile, Tealeaf CX Mobile, and IBM Xtify enable human interaction for engage while IBM MessageSight enables machine to machine (M2M) communications. Meanwhile, the Now Factory provides big data insights to support the transform entry point. Emptoris Rivermine Telecom expense management, IBM Endpoint Manager, IBM Security Access Manager, Trusteer end point security, and IBM Urban Code release automation are part of the optimize entry point.
- Mobile management is a critical function for successful BYOD and IBM's Mobile First strategy. MaaS360 provides a cloud based mobility management platform and an on-premises version will be available shortly. The solution is policy based to support a wide range of BYOD security and privacy requirements. MaaS360 supports mobile device management (MDM), mobile content management, and mobile applicant management including containerization.
(POV):
The acquisition of MaaS360 allows IBM to cover three key approaches to mobile management and security: secure transactions, containers, and mobile device management. MDM enables organizations to secure the device through bio-metrics, enrollment, configuration, monitoring, provisioning, and wiping. If successful, customers will find that MaaS360 can decrease the time and cost of supporting BYOD and simplify the overall approach to MDM.
- Customers and prospects can purchase from a trusted supplier. Over 100 vendors provide enterprise mobile management (EMM). The mobility management space is crowded. Most offerings come from poorly capitalized startups or vendors with limited distribution networks.
(POV): Customer and prospects fear startups going belly up. While MobileIron and Airwatch have pulled ahead from the pack, customers can expect rapid consolidation in the market. Citrix's acquisition of Zenprise foreshadowed the EMM market consolidation. Buyers can expect larger vendors such as Apple, Amazon, Google, Intel, Microsoft, Oracle, SAP, Salesforce.com, Symantec, VMWare and others to make acquisitions to complete their mobility footprints.
Figure 1. IBM's Mobile First Strategy Mixes Acquisitions With Organic Solution Development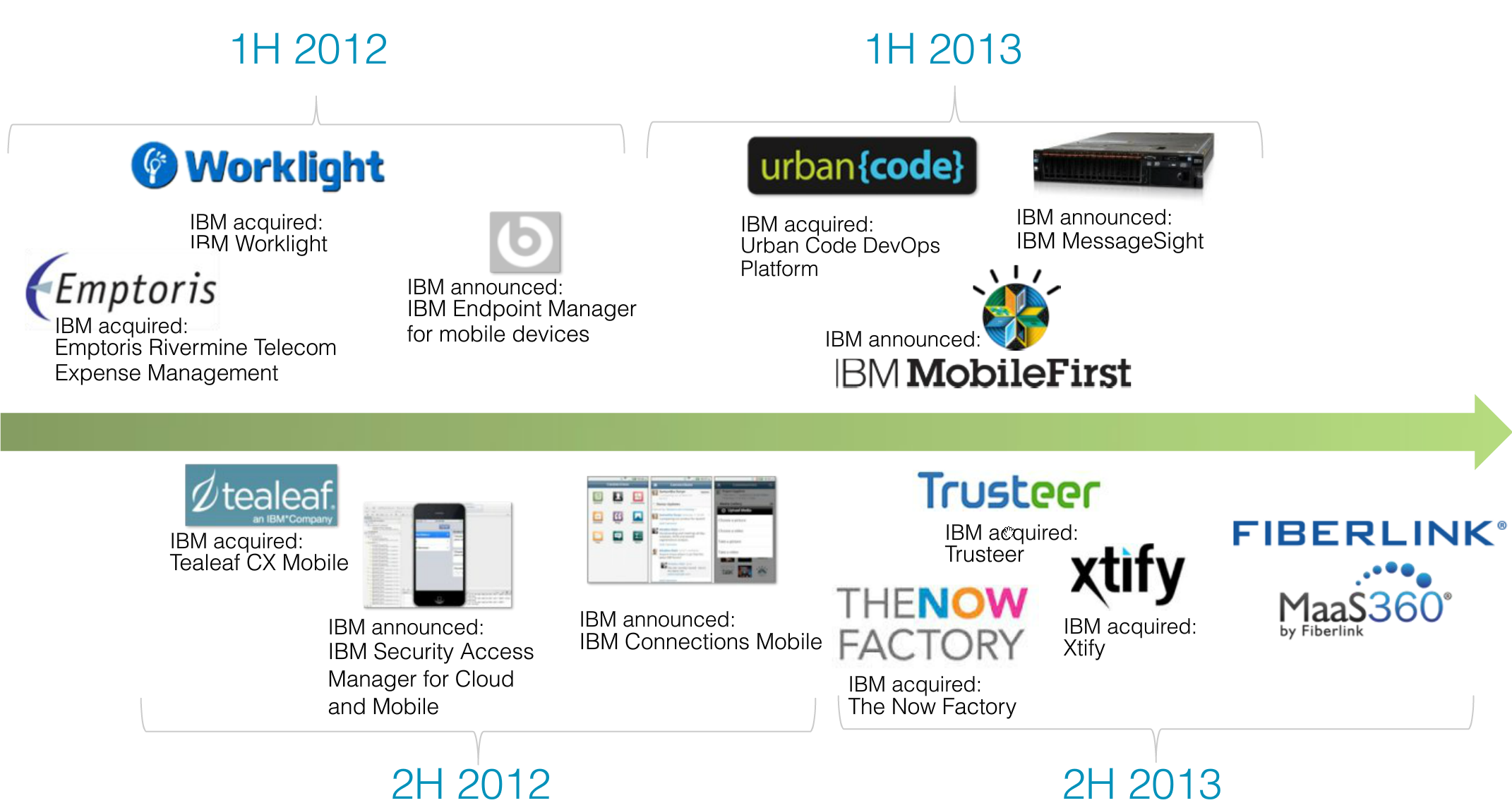
Source: IBM
The Bottom Line: Consolidation Is Good For Customers and Prospects
Mobility remains the wild west of applications development and consumerization of technology. As the stakes get higher, organizations seek integrated mobility suites. The shift to digital business requires cost effective and scalable mobility. As mass consolidation of mobile vendors continues, buyers will gain scale and stability from integrated mobility suites. Buyers expect to write once, deploy anywhere. Organizations expect security to be pervasive yet simple to support multiple end points. Consolidation will once again deliver the scale required for enterprises to quickly innovate and standardize on key platforms.
Your POV.
Are you looking at a mobile strategy? Do you see the link between mobility and digital business? Add your comments to the blog or reach me via email: R (at) ConstellationR (dot) com or R (at) SoftwareInsider (dot) com.
Please let us know if you need help with your mobility and Digital Business transformation efforts. Here’s how we can assist:
- Assessing mobile readiness
- Developing your digital business strategy
- Vendor selection
- Implementation partner selection
- Connecting with other pioneers
- Sharing best practices
- Designing a next gen apps strategy
- Providing contract negotiations and software licensing support
- Demystifying software licensing
Related Resources
- Tuesday’s Tip: Understand The Five Generation Of Digital Workers and Customers
- Monday’s Musings: The Chief Digital Officer In The Age Of Digital Business
- Slide Share: The CMO vs CIO – Pathways To Collaboration
- Event Report: Metaio’s #InsideAR Conference Hails The Future Of An Always On, Always Augmented Reality
- News Analysis: Avangate Acquired By Francisco Partners For Matrix Commerce Capabilities
- Event Report: CRM Evolution 2013 – Seven Trends In The Return To Digital Business And Customer Centricity
- Research Summary And Speaker Notes: The Identity Manifesto – Why Identity Is At The Heart of Digital Business
- News Analysis: Kana Express 13 Addresses Omni-Channel Customer Service for Mid-Market
- News Analysis: Zuora Raises $50M Series E Round, Rides #MatrixCommerce Wave
- Event Report: CRM Evolution 2013 – Seven Trends In The Return To Digital Business And Customer Centricity
- Monday’s Musings: Four Elements for A #SharingEconomy Biz Model In #MatrixCommerce
- Tuesday’s Tip: Why Context Matters – Forget Real-Time, Achieve Right-Time
- Monday’s Musings: Balancing The Six S’s In Consumerization Of IT
- Monday’s Musings: A Working Vendor Landscape For Social Business
- Research Report: The Upcoming Battle For The Largest Share Of The Technology Budget Part 1
- Research Report: How The Five Pillars Of Consumer Tech Influence Enterprise Innovation
- Best Practices: Five Simple Rules For Social Business
Reprints
Reprints can be purchased through Constellation Research, Inc. To request official reprints in PDF format, please contact Sales .
Disclosure
Although we work closely with many mega software vendors, we want you to trust us. For the full disclosure policy, stay tuned for the full client list on the Constellation Research website.
* Not responsible for any factual errors or omissions. However, happy to correct any errors upon email receipt.
Copyright © 2001 – 2013 R Wang and Insider Associates, LLC All rights reserved.
Contact the Sales team to purchase this report on a a la carte basis or join the Constellation Customer Experience!
 R "Ray" Wang
R "Ray" Wang R "Ray" Wang
R "Ray" Wang